Latest from our business, security
and technology blog
Search the blog:
Secure Yourself this Summer! How to Holiday with Peace of Mind
Summer is here! And if you’re about to jet off on holiday, IT security is probably the last thing on your mind. Thoughts of malware, spear-phishing and anti-virus are perhaps not as high on your agenda as sun, sea and sangria.
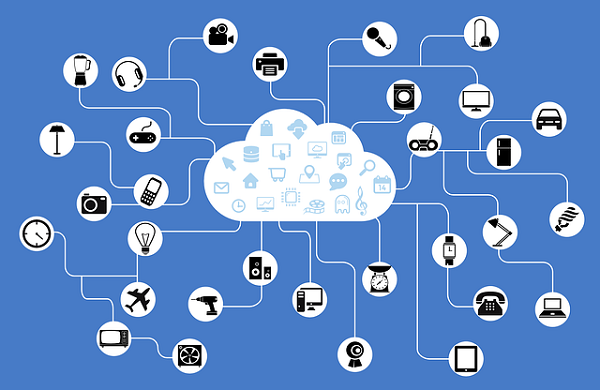
The Ever-Growing Attack Surface of IoT: Your Questions Answered
The impact of the Internet of Things is already making itself felt in our homes and in our everyday lives. This means an ever-growing threat for businesses as they try to keep pace with the new threats these devices present.
Grant McGregor Ranked Among World’s Most Elite 501 Managed Service Providers
We’re delighted to let you know that we’ve been named as one of the world’s premier managed service providers on the prestigious 12th annual Channel Futures MSP 501 rankings.
One Year On from GDPR: What’s Changed?
The General Data Protection Regulation (GDPR) came into effect on May 25, 2018. At the time it was heralded as a major change in the way individuals and organisations will think about – and collect, manage and secure – data.
Doubling up: why two-factor authentication is your next step in digital security
We’ve written about the need for additional layers of security for passwords, especially given the increased targeting of Microsoft’s Office 365 as more and more businesses and individuals migrate to the cloud, especially for email.
Outlook – Cloudy
We recently published an article relating to email and the evolution of cybercrime and another referring to the rising popularity of Microsoft’s Office 365 suite and the growing security risks associated with it.
Are Your Websites and Applications Secure?
What are you doing to secure your business website and other web applications used in your business? If you run local browser (web) applications, they are probably secured with a variety of techniques, including firewalls, regular patching and network monitoring. But what happens when you are...
From Spam to Phish – Cyber Crime on a Plate
Email – love or hate it as a form of communication, it touches most of us everyday and shows no signs of going away. This is especially true in the workplace where it hasn’t yet been dislodged by the various messaging apps as the preferred medium to send information.
How to Address the Dangers of Personal Devices for Work
What happens when an employee downloads a virus onto one of their personal devices that you have allowed access your company systems? Grant McGregor takes a look at an emerging weak spot in many companies’ defences.