Latest from our business, security
and technology blog
Search the blog:
The 7-Step Plan for Small Businesses for Essential Cyber Security
We discussed in an earlier blog how 80% of cyber-attacks could be prevented, simply by putting simple cyber security controls in place.
An Introduction to GDPR: Give Data Proper Respect!
The General Data Protection Regulation (GDPR) is getting a lot of column space, yet many businesses still have their head in the sand when it comes to its implications. We bust some myths and tell you what you need to know.
You’re Not Too Small to Be a Victim: The Obvious IT Security Fails Small Businesses Can Avoid
The Rise of Personally-Targeted Spear-Phishing Attacks & How to Defend Yourself From Them...
As we all become more wary about the tell-tale signs of a phishing email attack, criminals are turning to a more targeted approach to email scamming: the spear-phishing attack.
Your IT perimeter: where is it and how do you best defend it?
Gone are the days when the limits of your security cordon were the walls of the datacentre. Now, it isn’t the stray floppy disk or errant memory stick we need to worry about – many of us are wondering where the limits of our IT perimeter are.
Is the Password Still Relevant to Control Identity and Access to Your IT Systems and Data?
A lot of people believe that the password is an invention of the age of computing, a necessary part of securing IT systems from hackers and other malevolent forces – intentional or unintentional. In truth, the password is about as old as human civilisation.
Is Your Disaster Recovery Plan & Process Up to Scratch?
In recent years, the IT landscape has been transformed by digitalisation, Cloud, social and mobile – probably with significant impact on what a business-critical system looks like and what constitutes an IT disaster for your business.
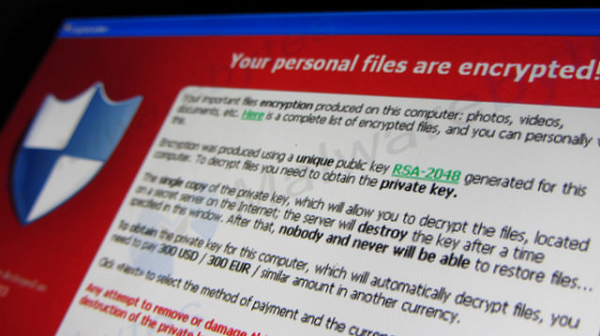
How to Protect Your Business Against Cyber-Attacks and Data Theft
Wow! Quite a weekend of news around Cyber Security... This was an article we had written a couple of weeks ago now and had scheduled for publication today just for the sake of offering our readers and supported end-users ongoing education about cyber security and playing your part...
5 Top Tips for Handling Confidential Information in Your Business
When handling confidential information in your business, whether it's relating to your customers or employees, you have a duty to take the necessary steps to protect it. Failure to ensure that data is properly protected and in accordance with the law can lead to lawsuits as well as damage to your...