Latest from our business, security
and technology blog
Search the blog:
Stop! And think, before you act on that email
How many times a day do you respond to an email without really thinking about its contents?
Should your users be using Microsoft Edge Password Manager?
In this blog, our team considers another of Microsoft’s technologies bundled with your Microsoft 365 subscription and asks: should your users be using Microsoft Edge Password Manager?
How to implement multi-factor authentication
Multi-factor authentication (MFA) adds an extra layer of protection for your network access and user accounts. It costs little or nothing and is easy to implement – so, if you haven’t already, it’s a good idea to implement MFA.
Agencies warn of Russian hacker threat on MFA
New warnings have been issued by US Federal agencies about the increased threat of Russian cyber attackers. The latest warning pertains to multi-factor authentication. Please read on for more details. The US Cybersecurity and Infrastructure Security Agency (CISA) has issued a new security alert in...
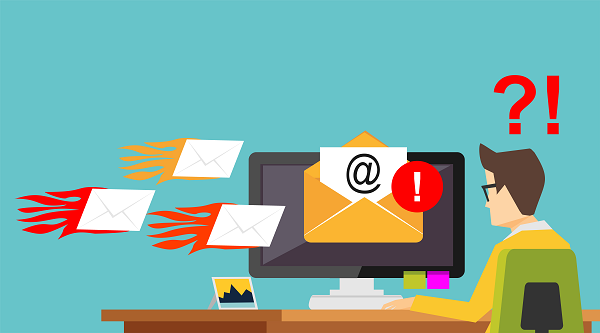
Microsoft blocks 1,000 malicious emails a second
Microsoft’s recently revealed that more than 35.7 billion malicious emails were sent to its customers last year. Fortunately for us, the tech giant blocked 1,000 of these malicious emails every second of 2021. That’s about 31.5 million seconds.
What is Zero Trust and Should I Be Implementing It?
The IT world is full of acronyms and strange phrases. “Zero Trust” is one of the latest to be bandied about, but what does it mean? And is it something your organisation needs to be thinking about? Zero Trust is a model for IT security. Although it is not a new concept, there is an increasing...
How to ensure web applications used in your business are secure
What are you doing to secure your business website and other web applications used in your business? If you run local browser (web) applications, they are probably secured with a variety of techniques, including firewalls, regular patching and network monitoring. But what happens when you are...
Why You Should be Using 2 Factor Authentication Right Now!
According to the Verizon 2019 Data Breach Investigations Report, 62% of breaches not involving an Error, Misuse, or Physical action (in other words, wounds that weren’t self-inflicted) involved the use of stolen credentials, brute force, or phishing.
On the Blacklist
The National Cyber Security Centre says maintaining a password blacklist is an essential part of good password security. We take a look at what should be on your blacklist and how to go about enforcing it.